Overview
The article addresses a critical issue in the realm of information security: the necessity of effective data limiting practices. IT managers must implement robust strategies to safeguard sensitive information and ensure compliance with regulations. This necessity is underscored by proven methodologies such as:
- Information classification
- Access controls
- Regular audits
These strategies not only bolster security but also mitigate breach risks and enhance operational efficiency within organizations. By adopting these best practices, organizations can significantly improve their security posture and operational integrity.
Introduction
In an age where data is often deemed the new oil, the practice of data limiting emerges as a vital strategy for organizations seeking to protect sensitive information while ensuring compliance with ever-evolving regulations.
For IT managers, understanding and implementing effective data limiting techniques is not merely a best practice; it is essential for safeguarding against data breaches and maintaining operational efficiency.
As industries grapple with the financial repercussions of inadequate data management—where the cost of data breaches can soar into millions—the need for robust data governance becomes increasingly apparent.
This article delves into the significance of data limiting, exploring proven strategies, tools, and the future trends that will shape the landscape of data privacy and security in organizations across various sectors.
Understanding Data Limiting: An Overview for IT Managers
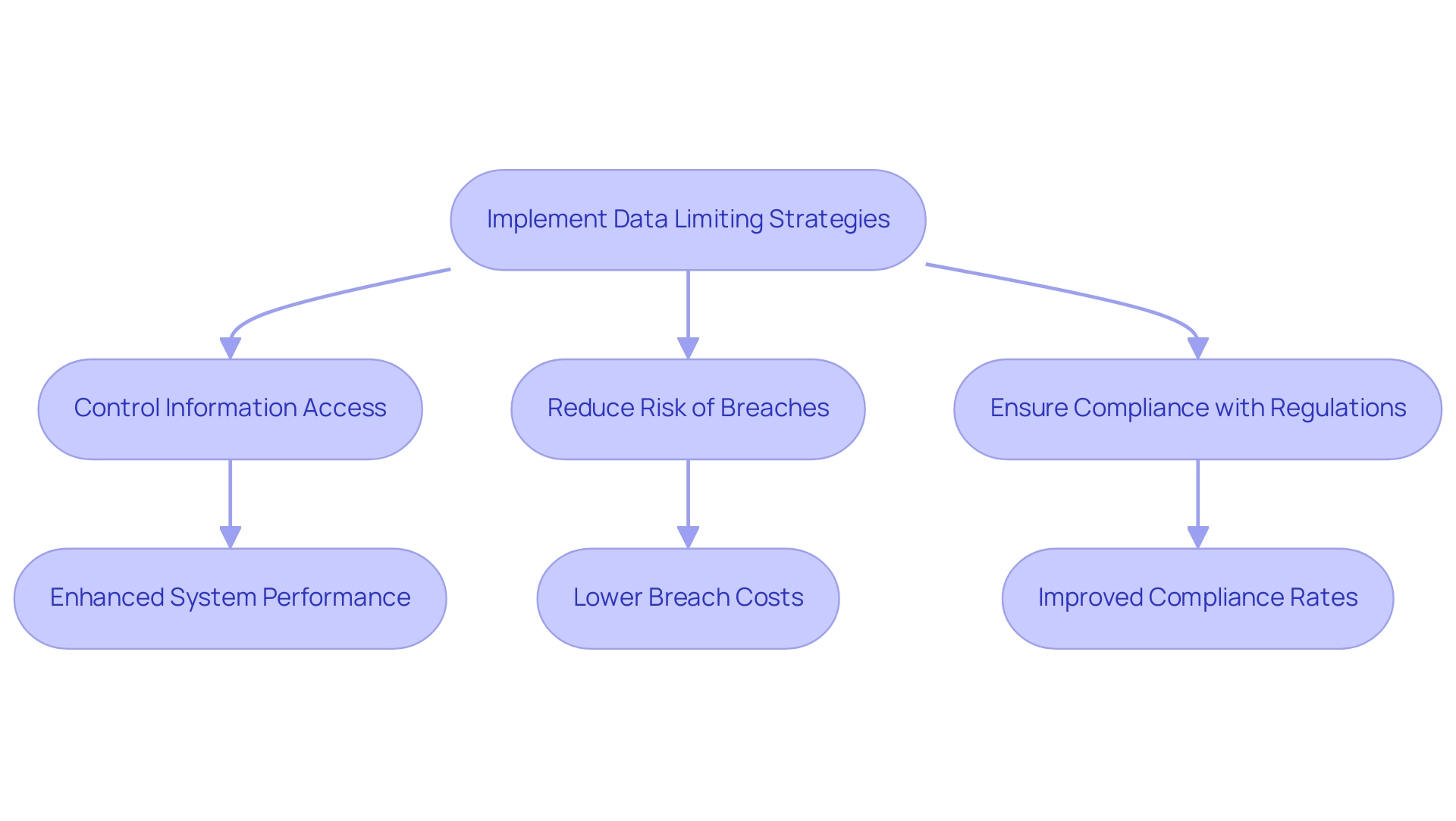
Data limiting is a crucial procedure that entails controlling the amount of information available or handled within a company, especially in sectors where privacy and protection are paramount. For IT managers, implementing effective data limiting strategies is vital for managing information flow, reducing the risk of breaches, and ensuring compliance with regulatory standards.
Research shows that organizations with fully deployed security AI and automation incur an average breach cost of $3.60 million, significantly lower than the $5.36 million faced by those lacking such measures. This stark contrast underscores the financial implications of robust information management practices, including restrictions, as they directly contribute to lowering breach expenses.
By adopting data limiting techniques, IT managers can not only safeguard sensitive information but also enhance system performance. Data limiting, by restricting access to information, prevents overload and ensures that only essential data is processed, leading to improved operational efficiency. Furthermore, with the global information privacy software market projected to grow from $2.76 billion in 2023 to $30.31 billion by 2030, the demand for effective privacy technologies, including data limiting measures, is on the rise.
This trend indicates that IT managers must evolve their strategies to meet changing market demands.
Successful implementations of information restriction strategies have been observed across various organizations. For example, Masha Komnenic, [an Information Security and Data Privacy Specialist, has been instrumental in assisting small and medium-sized enterprises in achieving compliance with privacy regulations. Her expertise in auditing and implementing information restriction practices has significantly bolstered protective measures, ensuring businesses meet legal standards.
The outcomes of her methods include improved compliance rates and reduced instances of breaches, highlighting the tangible benefits of information restriction.
The importance of data limiting extends beyond compliance; it is a fundamental component of privacy and protection. With 91% of companies acknowledging the need to reassure customers about information usage, the implementation of data limiting practices becomes increasingly critical. As André Loranger, Chief Statistician of Canada, states, “Organizations must prioritize data limiting to build trust and ensure the safety of their operations.”
By prioritizing data limiting, IT managers can cultivate a culture of security and trust within their organizations, ultimately leading to a more resilient and compliant operational framework.
The Importance of Data Limits in Regulated Industries
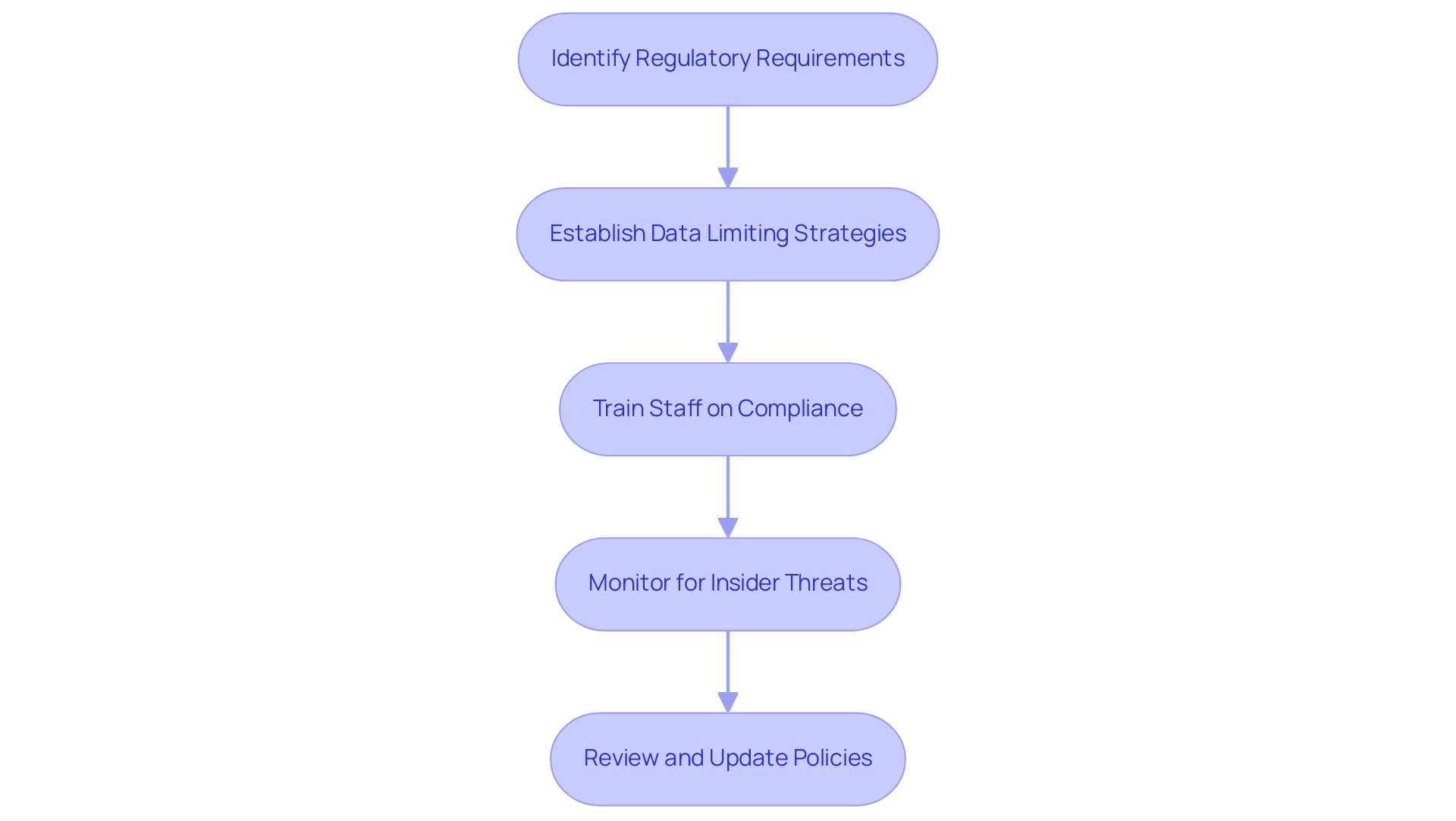
In regulated sectors such as banking and healthcare, establishing limits on information is not just a best practice; it is a legal imperative. Adhering to regulations such as GDPR and HIPAA requires strict controls over access and usage. By implementing clear data limiting strategies, IT managers can effectively restrict sensitive content to authorized personnel only, significantly reducing the risk of breaches. This proactive approach not only protects the organization but also fosters trust among customers and stakeholders.
Statistics reveal that organizations with fully implemented protective AI and automation face an average breach expense of $3.60 million, underscoring the financial repercussions of inadequate information management. Additionally, a significant portion of breaches in healthcare can be traced back to insider threats, encompassing both accidental and malicious negligence. The case study titled “Insider Threats in Healthcare” highlights the prevalence of these threats and their impact on HIPAA compliance, emphasizing the urgent need for enhanced training and security practices to mitigate such risks.
Expert insights suggest that organizations can achieve compliance with GDPR and HIPAA through effective data limiting strategies. Compliance officers consistently stress the importance of adhering to legal requirements for data limiting, especially in sectors where sensitive information is prevalent. As Rick Stevenson noted, “173 countries have ISO members representing them,” which underscores the global context of compliance challenges.
Furthermore, as we approach 2025, the landscape of information limits in regulated industries is continuously evolving, making it essential for IT managers to remain informed and proactive in their governance approach. Notably, 67% of Americans are unaware of their country’s privacy and information protection regulations, complicating compliance efforts for organizations. How can your organization navigate these challenges effectively?
Proven Strategies for Effective Data Limiting
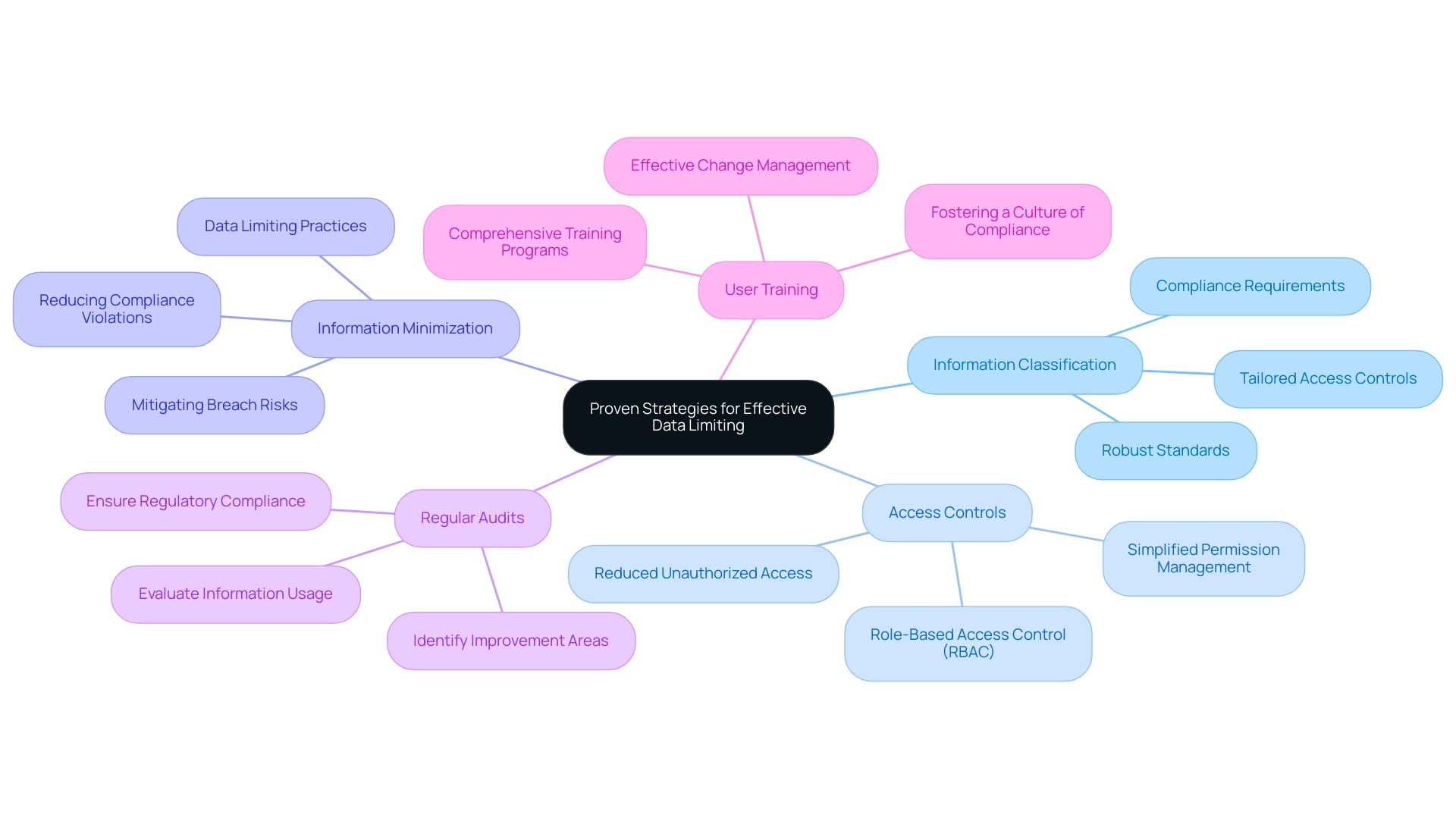
To effectively limit information usage, IT managers can adopt several key strategies:
- Information Classification: A robust information classification standard is essential for protecting sensitive details and meeting compliance requirements. By categorizing information based on its sensitivity and importance, organizations can tailor access controls to ensure that only authorized personnel can access critical information. This is particularly crucial given that phishing attacks account for more than 80% of reported incidents, highlighting the necessity for strict information management practices.
- Access Controls: Role-based access controls (RBAC) significantly enhance information protection. By assigning permissions according to user roles, organizations can substantially reduce the risk of unauthorized access to sensitive information. This approach not only strengthens security but also simplifies the management of user permissions. As noted by Gustavo Estrada from BC Provincial Health Services Authority, Avato has the ability to simplify complex projects, which can be crucial when implementing such controls.
- Information Minimization: An information minimization strategy entails gathering and retaining only the information necessary for specific business objectives. This practice not only reduces the overall footprint of information through data limiting but also mitigates the risks associated with breaches and compliance violations. With 43% of spoofing attacks impersonating Microsoft, minimizing information exposure is critical in safeguarding against such threats.
- Regular Audits: Regular audits are essential for evaluating information usage and ensuring adherence to established data limiting. These audits help identify areas for improvement and enable entities to make necessary modifications to their management practices. Frequent audits also play a vital role in ensuring that the entity complies with regulatory standards and safety protocols.
- User Training: Investing in comprehensive training programs is crucial to ensure that employees are proficient with Avato’s hybrid integration platform and understand the importance of limiting information and best practices for handling it. This training should clearly convey the significance of regulatory adherence and audits, fostering a culture of compliance within the entity. Applying effective change management techniques, such as transparent communication and support throughout the transition, will further facilitate the shift to new systems and encourage a culture of innovation.
By implementing these techniques, IT managers can enhance their entity’s information protection stance, effectively utilizing data limiting to restrict information usage and ensure adherence to regulatory standards. The impact of role-based access controls on information protection is significant, as they not only safeguard sensitive details but also improve access management procedures. Case studies have demonstrated that organizations employing effective classification and access control strategies experience a notable reduction in security incidents, reinforcing the importance of these best practices in IT management.
Tools and Technologies for Monitoring Data Limits
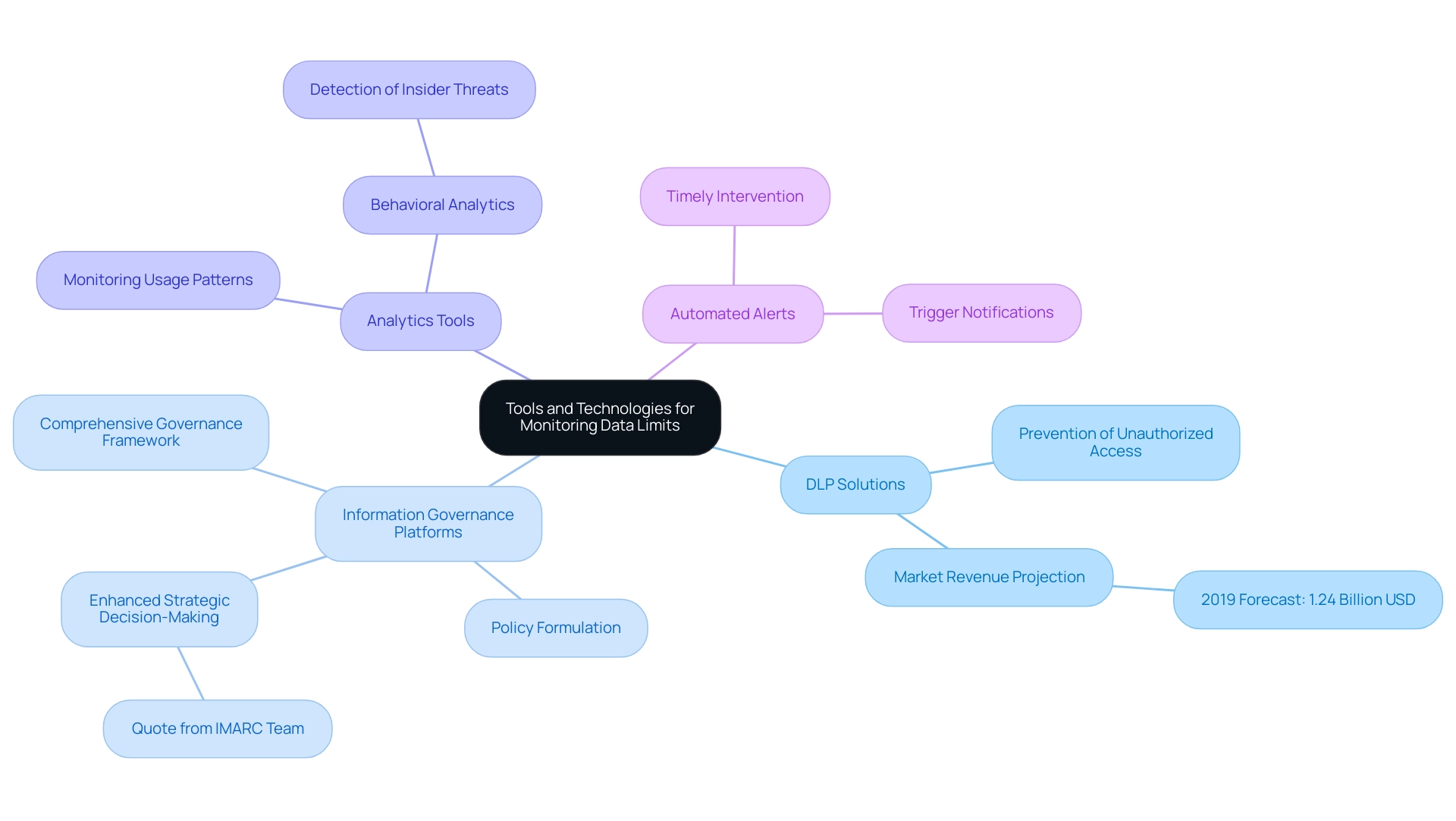
To effectively monitor and enforce data limits, IT managers must leverage a variety of advanced tools and technologies specifically designed to enhance data governance and security.
- Information Loss Prevention (DLP) Solutions are indispensable for monitoring usage and preventing unauthorized access or sharing of sensitive information. The DLP market revenue projection for 2019 was 1.24 billion U.S. dollars, highlighting the growing importance of investing in these solutions to safeguard organizational information.
- Information Governance Platforms establish a comprehensive governance framework, enabling organizations to formulate clear policies regarding access and usage. This structured approach not only boosts compliance but also promotes accountability across departments. As noted by the IMARC Team, “The depth of analysis, precision of information, and actionable recommendations have greatly enhanced our strategic decision-making,” illustrating the effectiveness of these platforms.
- Analytics Tools empower IT managers to monitor usage patterns adeptly. By identifying unusual trends, organizations can proactively address potential issues before they escalate, ensuring the integrity and security of information. Behavioral analytics is emerging as a critical feature in advanced DLP solutions, assisting in the detection of unusual patterns that may signal insider threats.
- Automated Alerts are crucial for timely intervention. These notifications can be set to trigger when usage nears predefined limits, enabling IT managers to take swift corrective actions and maintain control over data-limiting resources.
Incorporating these tools into IT management strategies allows organizations to develop robust governance frameworks that not only protect sensitive information but also enhance operational efficiency. Avato’s competitive advantage stems from its reliable technology stack, which aids businesses in adapting to evolving demands while maximizing the potential of legacy systems. Expert reviews underscore the effectiveness of these platforms in mitigating risks associated with breaches and ensuring compliance with regulatory standards.
As the landscape of information governance continues to evolve, equipping IT managers with the right solutions will empower them to navigate the complexities of management effectively.
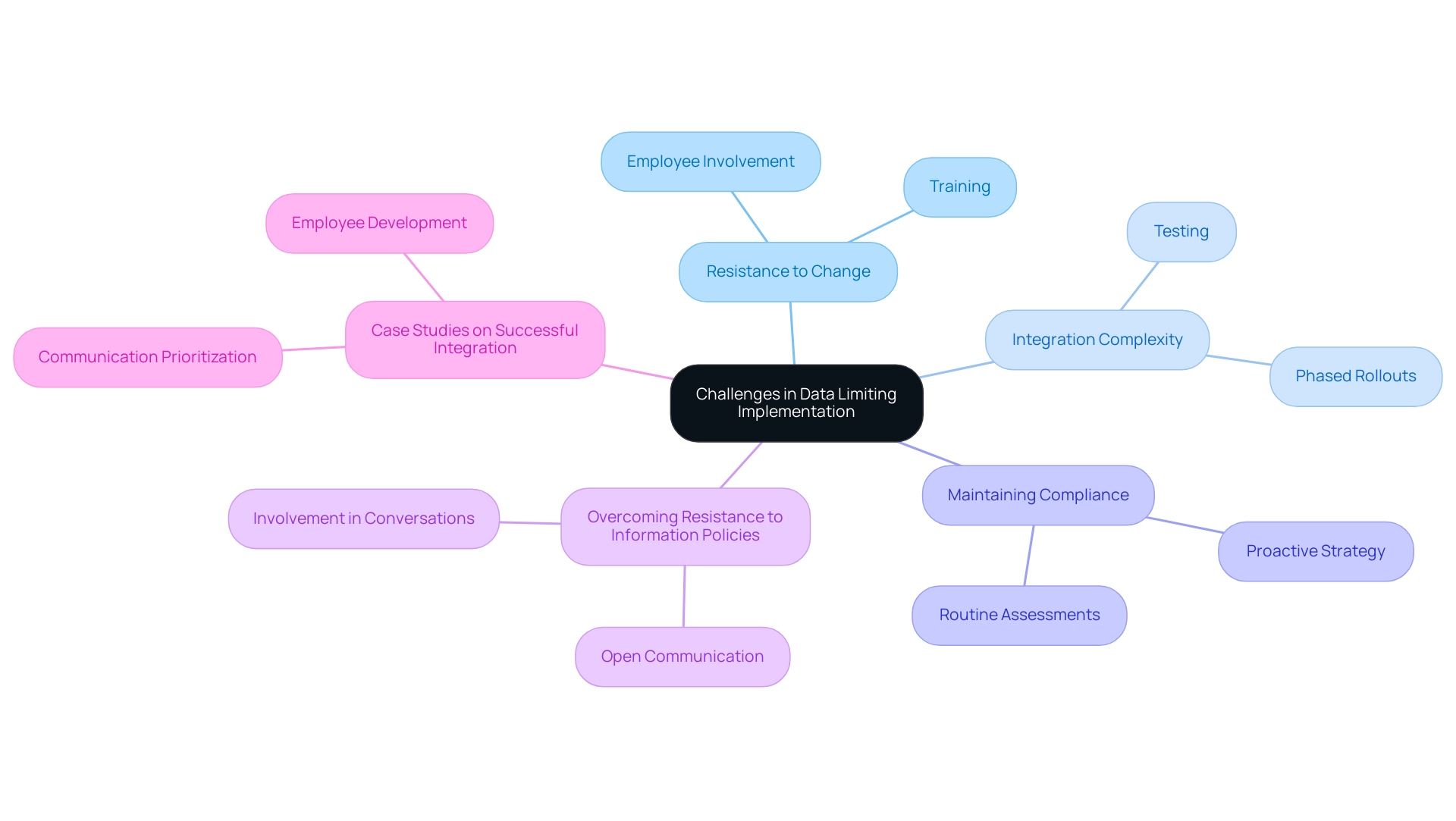
Overcoming Challenges in Data Limiting Implementation
Implementing information constraining strategies presents significant challenges that organizations must navigate effectively.
- Resistance to Change: One of the most common hurdles is employee resistance to new information policies. To mitigate this, involving employees in the development of these strategies is crucial. Offering thorough training that emphasizes the advantages of restriction can promote a culture of acceptance and comprehension. Statistics reveal that while 74% of leaders claim to involve employees in creating change strategies, only 42% of employees feel included. This gap underscores the importance of genuine engagement in the change process. As Gustavo Estrada noted, Avato simplifies complex projects and delivers results within desired time frames and budget constraints, which can help ease the transition.
- Integration Complexity: Ensuring that data limiting measures integrate seamlessly with existing systems can be complex and requires careful planning. Organizations should conduct thorough testing of new policies within existing frameworks and consider phased rollouts to minimize disruption. Successful integration not only enhances operational efficiency but also reinforces the value of the new policies to employees. Avato’s hybrid integration platform, designed for secure transactions and trusted by sectors like banking and healthcare, focuses on speed, security, and simplicity in integration, significantly aiding this process.
- Maintaining Compliance: Keeping up with evolving regulations can be daunting for many organizations. Routinely assessing compliance requirements and modifying restrictions on information accordingly is crucial. This proactive strategy assists in avoiding potential penalties and fosters trust with stakeholders by demonstrating a commitment to governance. Organizations that fail to manage change effectively can face substantial negative impacts on revenue and productivity, as highlighted in case studies on change management.
- Overcoming Resistance to Information Policies: Organizations often face resistance when implementing policies that involve data limiting measures. To address this, expert strategies suggest fostering open communication about the reasons behind these policies and their long-term benefits. Involving employees in conversations about information security and privacy can help alleviate concerns and encourage buy-in. Avato’s commitment to designing technology foundations enables enterprises to communicate effectively about the significance of governance.
- Case Studies on Successful Integration: Real-world examples illustrate the effectiveness of overcoming resistance to information restricting policies. Entities that prioritize communication and employee development during change initiatives have seen increased profitability and reduced operational costs. These successful transformations emphasize the potential for high returns on investment when information-restricting strategies are applied thoughtfully. Avato’s dependable, forward-looking technology framework aids companies in adjusting to evolving requirements, further improving the efficiency of these strategies.
By confronting these obstacles directly, companies can establish a robust structure for information management that not only boosts compliance and protection but also enables employees to embrace change.
Case Studies: Success Stories in Data Limiting
Numerous organizations have successfully adopted data limiting strategies, leading to significant improvements in security and compliance. For instance, a major bank implemented a robust classification system, effectively restricting access to sensitive customer information. As a result, this strategic action culminated in a remarkable 40% decrease in breaches within the first year of implementation.
In the healthcare sector, a prominent provider adopted role-based access controls, which not only strengthened information security but also enhanced operational efficiency. By streamlining access processes, the organization ensured that only authorized personnel could access critical details, thereby minimizing the risk of unauthorized exposure. However, many healthcare institutions face challenges in structuring clinical information for research purposes. The HITECH Act encourages the use of electronic health records (EHRs) but lacks financial incentives for improving information management.
As Yi Guo, an Academic Editor, aptly states, “Precision medicine enhances the ability to prevent diseases, promote health, and reduce health disparities in populations.” This underscores the importance of information security and compliance in healthcare, especially as organizations strive to protect sensitive data while improving patient outcomes. The integration of digital medicine, including AI and VR technologies, is essential for humanizing patient care and enhancing information accessibility, allowing healthcare providers to deliver more personalized and effective treatments.
These case studies illustrate the substantial impact that effective data limiting strategies can have on safeguarding sensitive information while simultaneously improving organizational workflows. With information breaches posing significant risks, the implementation of data limiting measures is increasingly vital for institutions aiming to protect their assets and comply with regulatory standards. Furthermore, improved training for healthcare workers and public awareness initiatives are crucial elements in the successful execution of information restriction strategies.
Avato’s hybrid integration platform, trusted by banks, healthcare, and government sectors, plays a pivotal role in this transformation. With features that support 12 levels of interface maturity, Avato accelerates secure system integration, enabling organizations to navigate the complexities of digital transformation effectively. As Tony Leblanc from the Provincial Health Services Authority noted, “Avato’s team is extremely professional and knowledgeable, making them a valuable partner in our integration efforts.”
This highlights Avato’s commitment to enhancing operational visibility and issue resolution, particularly for banking IT managers grappling with the challenges of legacy systems.
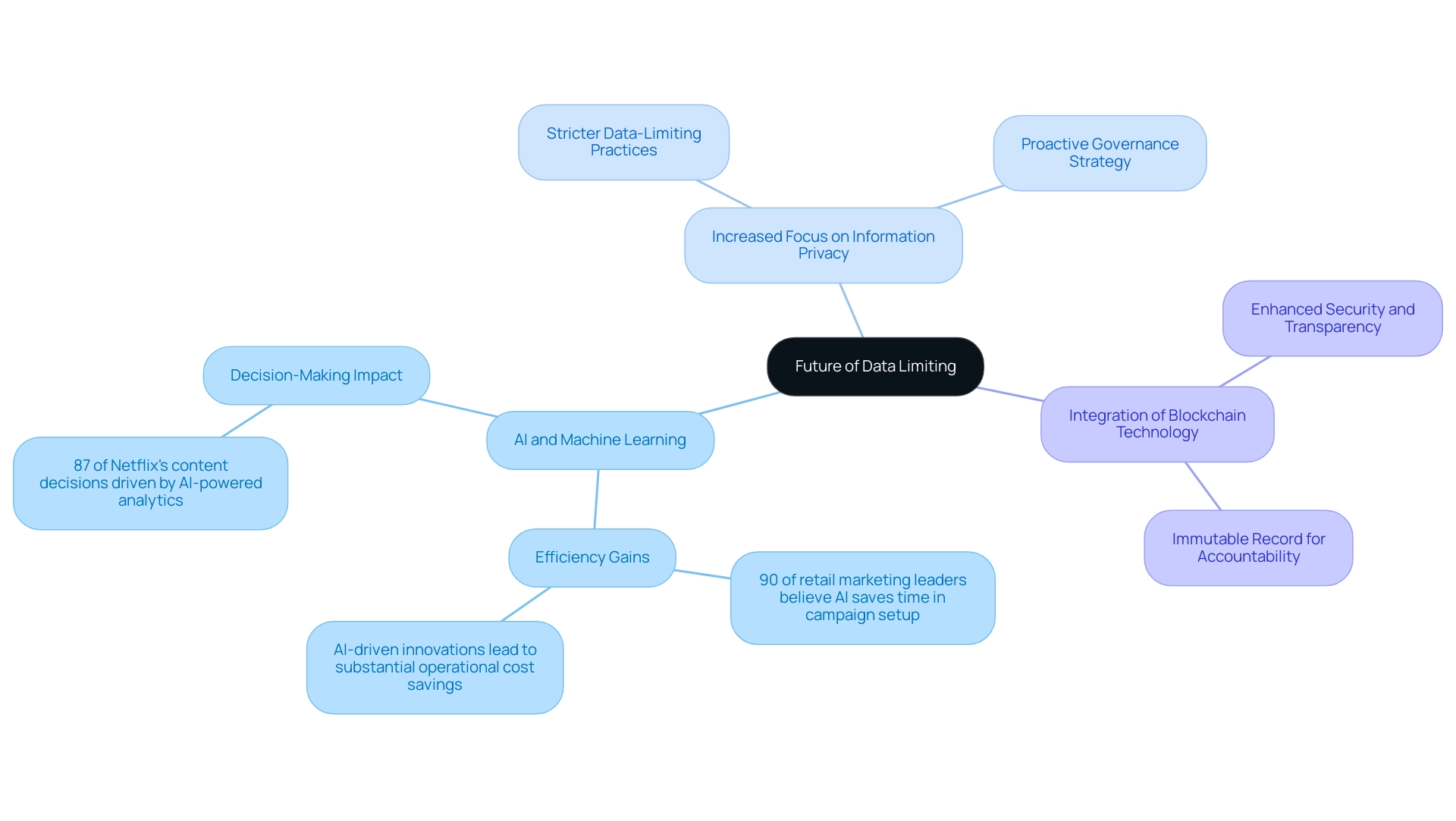
The Future of Data Limiting: Trends and Innovations
As information management evolves, several key trends are shaping the future of restrictions. AI and Machine Learning stand at the forefront of this transformation. These advanced technologies are set to revolutionize information monitoring and data limiting capabilities. By harnessing AI and machine learning, organizations can implement real-time adjustments based on user behavior and information usage patterns, significantly enhancing their ability to manage information effectively and responsively.
A statistic from 2024 reveals that nearly 90% of retail marketing leaders believe AI will save them time in campaign setup, showcasing the efficiency gains AI brings to information management. Increased Focus on Information Privacy is another critical trend. With rising concerns about privacy, organizations are compelled to adopt more stringent data-limiting practices. Adhering to evolving regulations necessitates a proactive governance strategy, ensuring sensitive information is safeguarded while maintaining operational efficiency.
According to IBM, only 37% of surveyed companies report taking measures to track provenance, underscoring the need for trustworthy AI in management. Integration of Blockchain Technology is gaining momentum as a method to bolster security and transparency. By leveraging blockchain, organizations can enforce data limiting more effectively and track usage, providing an immutable record that enhances accountability and trust in management practices.
This trend is further validated by case studies highlighting AI-driven innovations in business operations. Entities that leverage AI are projected to save substantial operational costs while enhancing decision-making processes.
These trends not only reflect the current landscape but also signal a shift toward secure, efficient, and compliant information management strategies, essential for navigating the complexities of modern information environments. The growing reliance on AI in decision-making is exemplified by Netflix’s report that 87% of its content decisions were driven by AI-powered data-limiting analytics, emphasizing AI’s critical role in these practices. Furthermore, companies and educational institutions are pivotal in bridging the AI skills gap by providing ongoing, skill-based education, ensuring organizations are well-equipped to adapt to these evolving trends.
Conclusion
Adopting effective data limiting practices is crucial for organizations striving to safeguard sensitive information while remaining compliant with regulatory standards. By implementing strategies such as:
- Data classification
- Role-based access controls
- Data minimization
IT managers can significantly reduce the risk of data breaches and enhance operational efficiency. The financial implications of inadequate data management cannot be overlooked; organizations with robust data governance measures are better positioned to mitigate breach costs and protect their assets.
The challenges associated with implementing data limiting strategies—such as resistance to change and integration with existing systems—can be effectively addressed through comprehensive training and proactive communication. Case studies illustrate that organizations prioritizing employee engagement and embracing advanced technologies, such as AI and machine learning, are more likely to succeed in their data governance efforts. As the landscape of data management continues to evolve, staying informed about emerging trends and innovations will empower IT managers to navigate complexities and enhance their organizations’ data security posture.
Ultimately, the commitment to data limiting is not just a regulatory requirement; it is a foundational element of building trust with customers and stakeholders. By fostering a culture of security and compliance, organizations can ensure they are well-equipped to face the challenges of the digital age. This makes data limiting an indispensable part of their operational strategy. As the future unfolds, embracing these practices will be key to achieving sustainable success in an increasingly data-driven world.

